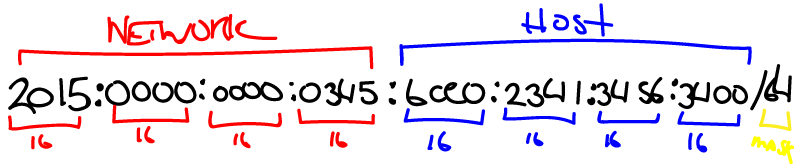
In my last post, I explained how to go about utilizing IPv6 prefix delegation using a Ubiquiti EdgeRouter 4, connected to an AT&T internet router that has IPv6 enabled on both the WAN and the LAN side. Now we’re going to walk through the basic firewall rules you need in place to protect your IPv6 network. And when I say basic, I mean the bare minimum to make sure the entire internet can’t get to your IPv6 devices, because if you’ve finished with the last post, your devices are likely open right now. 😐
Tag: AT&T Page 1 of 2
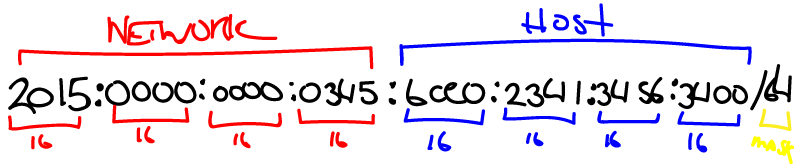
From the outset, it’s important to note that this is intended only for those who already have completed part one on the AT&T router, which is 1) enabling IPv6 on the LAN side and 2) enabling prefix delegation for the LAN. In addition, I’m using a Ubiquiti EdgeRouter 4 for my second firewall and this guide reflects that. However, if you’re using another IPv6 capable router, you may be able to glean settings from this and match them to your configuration.
*Disclaimer: If you enable this and mess with it in such a way as to make your network insecure, I’m not responsible for what may or may not happen due to your lack of security implementation related to traffic passing in and out of your internal network, i.e. if you get hacked, sorry, although I’ll gladly get employed to mitigate the situation ;).
Update: for a newer version of this information set within the Config Tree portion of the web interface of the EdgeRouter 4, read this post, with pictures and all! 🙂 https://davidwesterfield.net/2021/03/enabling-ipv6-prefix-delegation-on-att-internet-for-a-second-firewall/
I’m archiving this information for future reference because I (or others) may need it. This was extremely helpful in getting AT&T’s allotted IPv6 subnet(?) (properly called: delegated prefix) setup in my EdgeRouter 4, although I wound up having to use the web interface and configuring the same settings within the Config section. Without further ado (or a whole lot of ado below) here is Bradley Heilbrun’s explanation.
Update 8/3/2015:
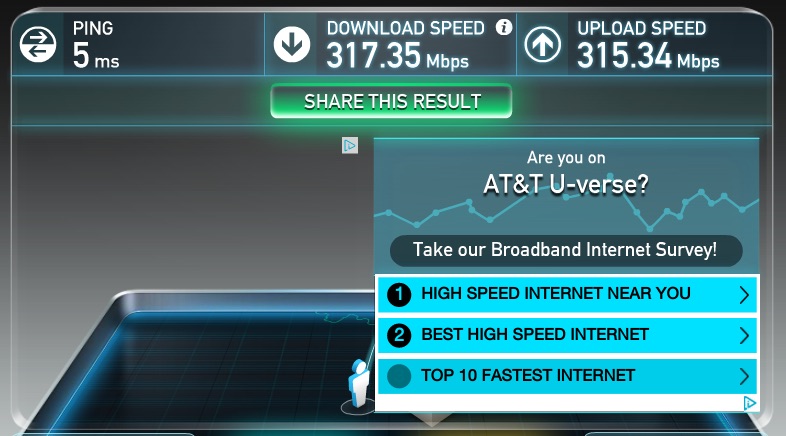
The speed has now been bumped up to 300 mbps up/down; so fast now, I need a new internal router/firewall 🙂
——————————————————————-
After events that occurred with AT&T on the technical and customer service sides back when I first moved into my new house, I wasn’t quite sure what to expect with changing over, once again, to new service. However, after all of the frustration and mind-boggling breakdowns in order processing and account bungling from a few months ago, this has been worth the wait.
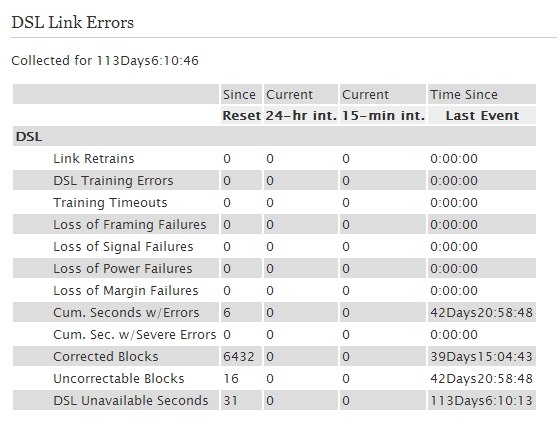
Though I haven’t proven this theory out yet I’ve been wondering since it seems to me to be a difference in stability. So my neighbors all around me have U-verse and have had all kinds of issues in which a U-verse tech has had to come out to resolve their issues. I’ve had basically none, with a couple of exceptions (area-wide drops). One neighbor had to have the line at the curb completely dug up and reset, but that was a different issue. When they setup my connection, I asked up front to run twisted pair from the outside to my router/gateway instead of using coax. As I understand it, unless I’m mistaken, the default is to use coax which, sure enough, all my neighbors have. As it pertains to VDSL2+ (the protocol U-verse uses), is twisted pair more stable than coax as a medium for delivery? I’m just curious, because that would be an easy thing to ask for at the beginning. I don’t know that this is the case, but I would be interested to see stats on that. Here are my numbers using twisted pair after 113 days of data/error collection:
 Apparently, after resetting the Motorola NVG510, it allows you right into the restricted areas without a password. Well, let me rephrase that in anecdotal terms. It let me in with no password. I was able to add NAT rules, change the wireless settings and number of other things. After a few minutes, it then locked me out and forced me to login. It’s been that way ever since fortunately, but why in the world would it allow me in without a password? And no, I didn’t have the password saved in my browser. On top of the connection issues I’ve experienced with this RG, the security issue described here adds one more layer of flakiness that deserves some attention. Anyone else out there experiencing this?
Apparently, after resetting the Motorola NVG510, it allows you right into the restricted areas without a password. Well, let me rephrase that in anecdotal terms. It let me in with no password. I was able to add NAT rules, change the wireless settings and number of other things. After a few minutes, it then locked me out and forced me to login. It’s been that way ever since fortunately, but why in the world would it allow me in without a password? And no, I didn’t have the password saved in my browser. On top of the connection issues I’ve experienced with this RG, the security issue described here adds one more layer of flakiness that deserves some attention. Anyone else out there experiencing this?
(FYI: When I first had Uverse setup, they allowed me to open SMTP port 25. This problem started when it was inadvertently blocked again recently. Long story short, there were other reports of this happening. Below is the process of trying to get it unblocked again.)
I have come to the realization tonight that my mail server has not been sending out emails since February 17th. I hopped on AT&T’s Uverse chat support and was informed (after connecting to a second tech for a possible different answer because, you know, not all techs know the same things) that AT&T is now blocking outbound SMTP port 25 for Uverse customers. I initially had the port opened on my account to allow outbound email for my mail server. But it doesn’t work now as of February 17. And if you want to have this port opened now, you must contact their Connectech team to unblock it. The number, as of now, is 1-866-294-3464, or you can apparently connect with their chat service here: https://chatnow.att.com/. If you send me an email directly right now, I’ll try to respond another way in the mean time.
—————————————————————
UPDATE 1: Okay this is rich. So I contacted Connectech via the chat app (which is an exe download, similar to TeamViewer), chatted with the tech about the problem and was asked if I had purchased a support plan. I said, no, I just need my port 25 opened again. He said, I can’t help you unless you have a package purchased (paraphrasing all of the aforementioned).
So let me get this straight: I already pay AT&T Uverse a larger amount of money for their technology (okay fine, whatever) than the other guys. I pay for support too when I have a problem, support that comes with my service. AT&T decides to block outbound port 25. To get it open, I can’t just call the regular support anymore. I have to call their outsourced “professional techs” to flip a switch. And in the process, at least pay them $20 more a month. You’ve gotta be kidding me? This is a new low for AT&T customer service. Ever heard of corporate communism? With their level of bureaucracy, red tape and hoops to jump through to get something done, for the one’s they’re supposed to be servicing, I can’t think of a better term. Or how about inefficiency?
—————————————————————
UPDATE 2: So after having blogged and tweeted this issue, I have received two responses from AT&T techs saying they can help. They asked me to direct message them on Twitter now with my account information. And although they are still tweeting others with issues, they will not respond. I don’t get it. Still waiting though …
—————————————————————
UPDATE 3: A social media guy (Mike A) from AT&T contacted me directly about the issue and is getting the ball rolling. Appreciate it!
—————————————————————
UPDATE 4: After receiving a call, I have yet to hear anything about a possible resolution or whether it is even still being looked at. I’ve called twice, left messages, with no response. Benefit of the doubt: could be very busy.
—————————————————————
UPDATE 5: Received a call from Mike A a little while ago at the social media team at AT&T and they let me know they have resolved the problem, port 25 is not being blocked anymore. There were apparently other reports of this happening and they are handling it on a case by case basis. Appreciate the help, Mike A, at @ATTTeamNatasha!
![]() I’m not sure at what point, but some time over the past week or two, my 2Wire 3800 HGV-B router was upgraded to new firmware (by AT&T of course), version 6.1.9.24 or rather 6.1.9.23-enh.tm. I’m not positive this fixed it or if AT&T upgraded their firewall policy, but for whatever reason, my NAT loopback works now. This has been a major complaint by both tech-ey customers and AT&T tech’s on various forums I’ve read ever since U-Verse started it’s roll-out a couple of years ago. It’s a pain to work around if you’re doing any port-forwarding on the outside of the firewall and then attempt to access those open ports from the inside of the network outward. Well, if you get upgraded to the latest version or get the latest firewall rules from AT&T, you should be good now.
I’m not sure at what point, but some time over the past week or two, my 2Wire 3800 HGV-B router was upgraded to new firmware (by AT&T of course), version 6.1.9.24 or rather 6.1.9.23-enh.tm. I’m not positive this fixed it or if AT&T upgraded their firewall policy, but for whatever reason, my NAT loopback works now. This has been a major complaint by both tech-ey customers and AT&T tech’s on various forums I’ve read ever since U-Verse started it’s roll-out a couple of years ago. It’s a pain to work around if you’re doing any port-forwarding on the outside of the firewall and then attempt to access those open ports from the inside of the network outward. Well, if you get upgraded to the latest version or get the latest firewall rules from AT&T, you should be good now.
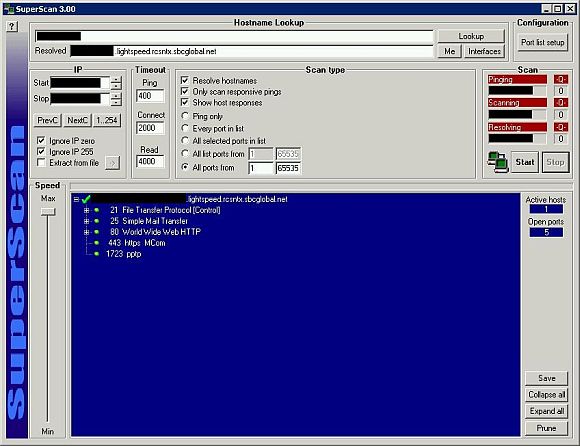
Public IP scanned from the internal network